Email authentication is the foundation of email deliverability. Without properly configured SPF, DKIM, and DMARC records, your email will land in the spam folder — or be rejected entirely. Since February 2024, Google requires all senders sending more than 5,000 emails per day to have all three authentication protocols configured. Microsoft and Yahoo have followed with similar requirements.
Yet authentication remains one of the most misconfigured aspects of email infrastructure. SPF records with too many DNS lookups, DKIM keys that are too short, DMARC policies stuck on “none” for years — these are problems we see on nearly every email audit we conduct. The good news is that proper setup takes less than an hour and protects your deliverability for the life of your domain.
91%
of cyberattacks start with email
3.4B
phishing emails sent daily
10x
better delivery with full auth
< 1 hr
to set up all three protocols
Free SPF / DKIM / DMARC Checker
Enter your domain and we'll look up your live DNS records via Cloudflare DNS, then flag what's missing or misconfigured. No data is sent to our servers.
Common DKIM selectors: google (Google Workspace), selector1 / selector2 (Microsoft 365), k1 (Mailchimp), default, mail.
This guide covers each authentication protocol in depth — the what, why, and exactly how to set it up. We will walk through SPF syntax and lookup limits, DKIM key generation and DNS publishing, DMARC policy progression from monitoring to enforcement, rDNS/PTR records, BIMI setup for brand logos, testing tools, and real-world DNS record examples with common troubleshooting scenarios.
At BulkEmailSetup, we configure complete email authentication for every dedicated server we provision. This guide shares the exact process we follow — so you can either implement it yourself or understand what a managed service should be doing for you.
Why Email Authentication Matters in 2026
The Authentication Stack
SPF, DKIM, and DMARC are three complementary protocols. Each verifies something different — DMARC ties them together with domain alignment.
SPF
IP-Based Verification
SPF = PASS
DKIM
Crypto-Based Verification
DKIM = PASS
DMARC
Domain Alignment Policy
DMARC = PASS
Final Decision
DMARC Verdict: PASS
SPF aligned + DKIM aligned = Email is authenticated
DMARC Alignment Requirement
DMARC passes if at least one of SPF or DKIM passes ANDthe passing protocol's domain aligns with the From header domain. Both strict (aspf=s) and relaxed (aspf=r) alignment modes are supported.
Email was designed in 1982 without any built-in authentication. The original SMTP protocol allows anyone to send an email claiming to be from any address — there is no verification that the sender is who they claim to be. This fundamental design flaw is why phishing, spoofing, and email fraud are still rampant decades later.
SPF, DKIM, and DMARC were developed over the following decades to retroactively add authentication to email. Together, they answer three critical questions that ISPs ask about every incoming email:
Without Authentication
- ✗Anyone can send email pretending to be your domain
- ✗ISPs treat your email as suspicious and unverified
- ✗Higher spam folder placement across all ISPs
- ✗Vulnerable to phishing attacks using your brand
- ✗No visibility into who is sending as your domain
- ✗Gmail marks email with a warning: 'This message may not be from who it claims'
- ✗Reduced open rates and engagement from trust signals
With Full Authentication
- ✓Only authorized servers can send as your domain
- ✓ISPs trust your email and deliver to the inbox
- ✓Significantly better inbox placement rates
- ✓Spoofing attempts are blocked or quarantined
- ✓DMARC reports show all sending activity for your domain
- ✓Gmail shows verified sender indicators
- ✓Higher engagement from trusted brand identity
Without Authentication
- ✗Anyone can send email pretending to be your domain
- ✗ISPs treat your email as suspicious and unverified
- ✗Higher spam folder placement across all ISPs
- ✗Vulnerable to phishing attacks using your brand
- ✗No visibility into who is sending as your domain
- ✗Gmail marks email with a warning: 'This message may not be from who it claims'
- ✗Reduced open rates and engagement from trust signals
With Full Authentication
- ✓Only authorized servers can send as your domain
- ✓ISPs trust your email and deliver to the inbox
- ✓Significantly better inbox placement rates
- ✓Spoofing attempts are blocked or quarantined
- ✓DMARC reports show all sending activity for your domain
- ✓Gmail shows verified sender indicators
- ✓Higher engagement from trusted brand identity
The Gmail 2024 Mandate
In October 2023, Google announced that starting February 2024, all senders sending more than 5,000 emails per day to Gmail addresses must have SPF, DKIM, and DMARC configured. Senders who do not comply see their email rejected with 550 error codes — not just spam-foldered, but outright blocked.
Microsoft and Yahoo followed with similar requirements throughout 2024. By 2026, email authentication is not a “best practice” — it is a hard requirement for email delivery. If you are sending bulk email of any kind — marketing, transactional, or cold outreach — and do not have full authentication configured, you are losing deliverability right now.
Authentication Is No Longer Optional
As of 2026, all major ISPs (Gmail, Outlook, Yahoo, Apple) require SPF and DKIM authentication. DMARC with at least a p=none policy is required by Gmail for bulk senders. Without these records, your email will be rejected with 550 errors — not just spam-foldered. This applies to all email, including transactional messages.
SPF (Sender Policy Framework) — Complete Setup Guide
SPF Validation Flow
When an email arrives, the receiving server checks whether the sending IP is authorized by the domain's SPF record in DNS.
Email Arrives
From: [email protected]
Extract Sender Domain
MAIL FROM → example.com
DNS TXT Lookup
dig TXT example.com
Parse SPF Record
v=spf1 ip4:192.0.2.0/24 include:_spf.google.com -all
Check Sending IP
Is 192.0.2.10 in allowed list?
PASS
IP is authorized
SOFTFAIL
IP not authorized (lenient)
FAIL
IP is not authorized
SPF Mechanism Reference
ip4:Allow IPv4 rangeinclude:Check another domainaAllow domain A recordmxAllow domain MX IPs-allFail all others~allSoft-fail all othersSPF is the first layer of email authentication. It tells receiving mail servers which IP addresses and servers are authorized to send email on behalf of your domain. When an ISP receives an email claiming to be from your domain, it checks your SPF record to verify that the sending server is authorized.
How SPF Works
SPF Record Syntax
An SPF record is a DNS TXT record published at the root of your domain. It follows a specific syntax with mechanisms that define authorized senders and a qualifier that defines the default policy.
| Mechanism | Syntax Example | What It Does |
|---|---|---|
| ip4 | ip4:203.0.113.10 | Authorizes a specific IPv4 address |
| ip4 range | ip4:203.0.113.0/24 | Authorizes an entire IPv4 subnet (CIDR notation) |
| ip6 | ip6:2001:db8::1 | Authorizes a specific IPv6 address |
| include | include:_spf.google.com | Includes another domain's SPF record (for third-party senders) |
| a | a:mail.yourdomain.com | Authorizes the IP that the A record resolves to |
| mx | mx | Authorizes IPs of your domain's MX servers |
| -all | -all | Hard fail: reject email from unauthorized IPs |
| ~all | ~all | Soft fail: accept but mark as suspicious (use only during testing) |
| ?all | ?all | Neutral: no policy (effectively useless, avoid this) |
Real-World SPF Record Examples
Example SPF Records
Simple — single server:v=spf1 ip4:203.0.113.10 -all
Multiple servers:v=spf1 ip4:203.0.113.10 ip4:198.51.100.20 -all
With Google Workspace and a dedicated SMTP:v=spf1 ip4:203.0.113.10 include:_spf.google.com -all
With multiple third-party services:v=spf1 ip4:203.0.113.10 include:_spf.google.com include:sendgrid.net include:mailgun.org -all
The 10-DNS-Lookup Limit
This is the single most common SPF configuration error. The SPF specification (RFC 7208) limits the total number of DNS lookups an SPF evaluation can perform to 10. Each include, a, mx, and redirect mechanism counts as one lookup. ip4 and ip6 mechanisms do not count because they do not require DNS resolution.
When your SPF record exceeds 10 lookups, the SPF evaluation returns a “permerror” result — which most ISPs treat as an SPF failure. This commonly happens when you use multiple third-party services (Google Workspace, SendGrid, Mailchimp, HubSpot, Salesforce) that each add their own include mechanism. Each include can itself contain nested includes, and they all count toward the limit.
| Mechanism | DNS Lookups | Counts Toward Limit? |
|---|---|---|
| ip4:203.0.113.10 | 0 | No — IP address is literal |
| ip6:2001:db8::1 | 0 | No — IP address is literal |
| include:_spf.google.com | 1+ (nested includes also count) | Yes |
| a:mail.yourdomain.com | 1 | Yes |
| mx | 1 (plus 1 per MX host) | Yes |
| redirect=otherdomain.com | 1+ | Yes |
| -all / ~all | 0 | No — qualifier, not mechanism |
Pro Tip
If you are running into the 10-lookup limit, replace include mechanisms with direct ip4 addresses where possible. For example, instead of include:sendgrid.net, find SendGrid's actual sending IPs and list them directly. This uses zero lookups instead of 3-4. The trade-off is that you must update your SPF record if the provider changes their IPs. Alternatively, use an SPF flattening service that automates this process.
DKIM (DomainKeys Identified Mail) — Complete Setup Guide
DKIM Signing & Verification
The sending server signs the email with a private key. The receiving server retrieves the public key from DNS to verify the signature has not been tampered with.
Sending Server
Email Body
Generate Hash
Sign with Private Key
Add DKIM-Signature Header
Email in Transit
Email in Transit
Receiving Server
Extract DKIM Header
DNS Lookup: Public Key
Decrypt Signature
Compare Hashes
Hash Match = DKIM PASS
Message integrity verified
Example DKIM-Signature Header
DKIM-Signature: v=1; a=rsa-sha256; d=example.com; s=selector1; h=from:to:subject:date; bh=abc123...; b=xyz789...
DKIM adds a cryptographic digital signature to every email you send. The receiving server verifies this signature against a public key published in your DNS. This proves two things: the email genuinely came from your domain, and the message was not altered in transit.
Unlike SPF (which verifies the sending server), DKIM verifies the message itself. This means DKIM survives email forwarding — when someone forwards your email, the DKIM signature remains valid because the message content has not changed. This is a critical advantage because SPF often fails on forwarded email.
DKIM Key Generation
DKIM uses asymmetric cryptography — a private key (kept on your server) signs outgoing email, and a public key (published in DNS) verifies the signature. You must generate a key pair of at least 2048 bits. Older 1024-bit keys are still accepted by most ISPs but are considered weak and will eventually be deprecated.
Publishing the DKIM Public Key in DNS
The public key from the generated key pair must be published as a DNS TXT record. The record name follows the format: selector._domainkey.yourdomain.com. The selector is a string you choose (commonly “default”, “s1”, or “google”) that allows you to have multiple DKIM keys for the same domain.
| Field | Value | Notes |
|---|---|---|
| Record Type | TXT | DKIM keys are published as TXT records |
| Record Name | default._domainkey.yourdomain.com | Replace 'default' with your chosen selector |
| Record Value | v=DKIM1; h=sha256; k=rsa; p=MIIBIjANBg... | The full public key from opendkim-genkey output |
| TTL | 3600 (1 hour) | Lower TTL during setup for faster propagation |
DNS Character Limit for DKIM Keys
A 2048-bit DKIM key is longer than the 255-character limit for a single DNS TXT record string. Most DNS providers automatically split the key into multiple strings within the same TXT record (using quoted strings). If your provider does not, you must manually split the key. Check that the published key matches by querying DNS and comparing with the generated key.
DKIM Header Anatomy
When your server signs an outgoing email with DKIM, it adds a DKIM-Signature header to the message. Understanding this header helps you troubleshoot DKIM failures. Here are the key fields:
| Tag | Meaning | Example Value |
|---|---|---|
| v= | DKIM version (always 1) | 1 |
| a= | Signing algorithm | rsa-sha256 |
| d= | Signing domain | yourdomain.com |
| s= | Selector (matches DNS record name) | default |
| c= | Canonicalization method | relaxed/relaxed |
| h= | Headers included in the signature | from:to:subject:date:message-id |
| b= | The actual signature (base64 encoded) | dkjfQOE73h2... |
| bh= | Body hash (hash of the email body) | 2jUSOH9Nhtk... |
DKIM Key Rotation
DKIM keys should be rotated every 6-12 months as a security best practice. Key rotation involves generating a new key pair, publishing the new public key with a different selector, configuring your server to sign with the new key, and eventually removing the old key from DNS.
Generate new key pair with a new selector
Use a new selector name (e.g., “s2” if your current selector is “s1”, or use a date-based selector like “mar2026”). Generate the key: opendkim-genkey -s s2 -d yourdomain.com -b 2048
Publish the new public key in DNS
Add the new TXT record as s2._domainkey.yourdomain.com with the new public key. Keep the old record in place — both selectors should exist simultaneously during transition.
Update your MTA to sign with the new selector
Update your OpenDKIM configuration (or equivalent) to use the new selector and private key. Restart the DKIM signing service. New outgoing email will now be signed with the new key.
Wait 7-14 days, then remove the old DNS record
Keep the old public key in DNS for 1-2 weeks after switching. This ensures any email still in transit or in recipients' inboxes can still verify the old signature. After two weeks, remove the old selector record.
DMARC (Domain-based Message Authentication, Reporting and Conformance)
DMARC is the policy layer that ties SPF and DKIM together. It tells receiving servers what to do when an email fails SPF and DKIM checks, and it provides a reporting mechanism that gives you visibility into all email being sent using your domain — including unauthorized senders.
DMARC is published as a DNS TXT record at _dmarc.yourdomain.com. It specifies a policy (none, quarantine, or reject), reporting addresses, and alignment requirements.
DMARC Policy Levels
DMARC offers three policy levels that control what happens when email fails authentication. You should progress through these levels gradually — starting with monitoring, moving to quarantine, and eventually enforcing full rejection.
p=none (Monitor)
- ✓No impact on email delivery
- ✓Collects DMARC reports only
- ✓Use during initial setup and warm-up
- ✓Identifies all senders using your domain
- ✓Safe starting point — cannot break email
- ✓Minimum 2-4 weeks at this level
p=quarantine (Enforce)
- ✓Failed email goes to spam folder
- ✓Legitimate email continues to inbox
- ✓Protects against most spoofing
- ✓Review DMARC reports before upgrading
- ✓Use pct= tag to apply gradually (start with 10%)
- ✓Minimum 2-4 weeks at this level
p=reject (Full Protection)
- ✓Failed email is outright rejected
- ✓Maximum protection against spoofing
- ✓The gold standard for email authentication
- ✓Only implement after thorough testing
- ✓Monitor reports to catch any legitimate failures
- ✓Enables BIMI logo display in supported clients
DMARC Record Syntax
| Tag | Required? | Example | Description |
|---|---|---|---|
| v=DMARC1 | Yes | v=DMARC1 | Protocol version (always DMARC1) |
| p= | Yes | p=quarantine | Policy: none, quarantine, or reject |
| rua= | Recommended | rua=mailto:[email protected] | Aggregate report destination (daily summaries) |
| ruf= | Optional | ruf=mailto:[email protected] | Forensic report destination (individual failures) |
| pct= | Optional | pct=25 | Percentage of failed email to apply policy to (default: 100) |
| sp= | Optional | sp=reject | Subdomain policy (inherits from p= if not set) |
| adkim= | Optional | adkim=s | DKIM alignment: s=strict, r=relaxed (default: r) |
| aspf= | Optional | aspf=r | SPF alignment: s=strict, r=relaxed (default: r) |
Real-World DMARC Record Examples
DMARC Records for Each Stage
Stage 1 — Monitoring (start here):v=DMARC1; p=none; rua=mailto:[email protected]; ruf=mailto:[email protected]
Stage 2 — Gradual enforcement (25% quarantine):v=DMARC1; p=quarantine; pct=25; rua=mailto:[email protected]
Stage 3 — Full quarantine:v=DMARC1; p=quarantine; rua=mailto:[email protected]
Stage 4 — Full reject (gold standard):v=DMARC1; p=reject; rua=mailto:[email protected]; adkim=s; aspf=s
DMARC Alignment Explained
DMARC introduces the concept of “alignment” — the requirement that the domain in the From header matches the domain verified by SPF or DKIM. This prevents attackers from passing SPF with their own domain while spoofing yours in the From header.
There are two alignment modes: relaxed (default) allows organizational domain matches (mail.yourdomain.com aligns with yourdomain.com), while strict requires an exact domain match. Relaxed alignment is sufficient for most setups and is more forgiving of legitimate sending patterns like subdomain senders.
Pro Tip
Use a DMARC reporting analysis tool like dmarcian, Postmark DMARC, or Valimail to process your DMARC aggregate reports. Raw DMARC reports are XML files that are nearly impossible to read manually. These tools parse the reports and show you exactly who is sending email as your domain, whether they pass authentication, and where failures occur.
DMARC Policy Progression — From None to Reject
DMARC Policy Progression
Never jump straight to reject. Gradually increase your DMARC enforcement while monitoring reports to avoid blocking legitimate email.
p=noneMonitor OnlyCollect reports, no action taken on failures
p=quarantine; pct=25Quarantine 25%Move 25% of failing emails to spam
p=quarantine; pct=100Full QuarantineAll failing emails go to spam
p=rejectFull ProtectionReject all unauthorized emails outright
8-15
Weeks total
p=reject
Final goal
rua + ruf
Reports throughout
Moving from p=none to p=reject is a multi-week process that should be driven by data from DMARC reports. Each stage gives you confidence that all legitimate email is properly authenticated before you enforce stricter policies that could block legitimate messages.
Deploy p=none and collect reports (weeks 1-4)
Publish your initial DMARC record with p=none and aggregate reporting. For 2-4 weeks, collect DMARC reports to identify all services sending email as your domain. You will likely discover third-party services (CRM, marketing tools, helpdesk) that need SPF/DKIM configuration.
Fix authentication for all legitimate senders
For each legitimate sender identified in DMARC reports, ensure SPF includes their sending IPs and DKIM is properly configured. Common third-party senders: Google Workspace, Microsoft 365, SendGrid, Mailchimp, HubSpot, Salesforce, Zendesk. Each must pass either SPF or DKIM with DMARC alignment.
Move to p=quarantine with pct=10 (week 5)
Start enforcement gradually by quarantining only 10% of failed email. Monitor DMARC reports for any legitimate email being quarantined. If none, increase pct to 25%, then 50%, then 100% over the following weeks.
Increase to p=quarantine; pct=100 (weeks 6-8)
Once you are confident all legitimate email passes DMARC, apply quarantine to 100% of failed email. Monitor for 2 weeks at this level before moving to reject.
Move to p=reject (week 9+)
The final step. Change your policy to p=reject to tell ISPs to outright reject unauthenticated email. This is the strongest protection against domain spoofing and is required for BIMI logo display.
The pct= Tag Is Your Safety Net
When moving from p=none to p=quarantine or p=reject, use the pct= tag to apply the policy to a percentage of failed email. Start at pct=10, then increase to 25, 50, and 100 over several weeks. This lets you catch misconfigured legitimate senders before they get blocked entirely.
rDNS (PTR Records) and BIMI Setup
Beyond SPF, DKIM, and DMARC, two additional authentication-adjacent protocols significantly impact deliverability: reverse DNS (rDNS / PTR records) and BIMI (Brand Indicators for Message Identification).
Reverse DNS (PTR Records)
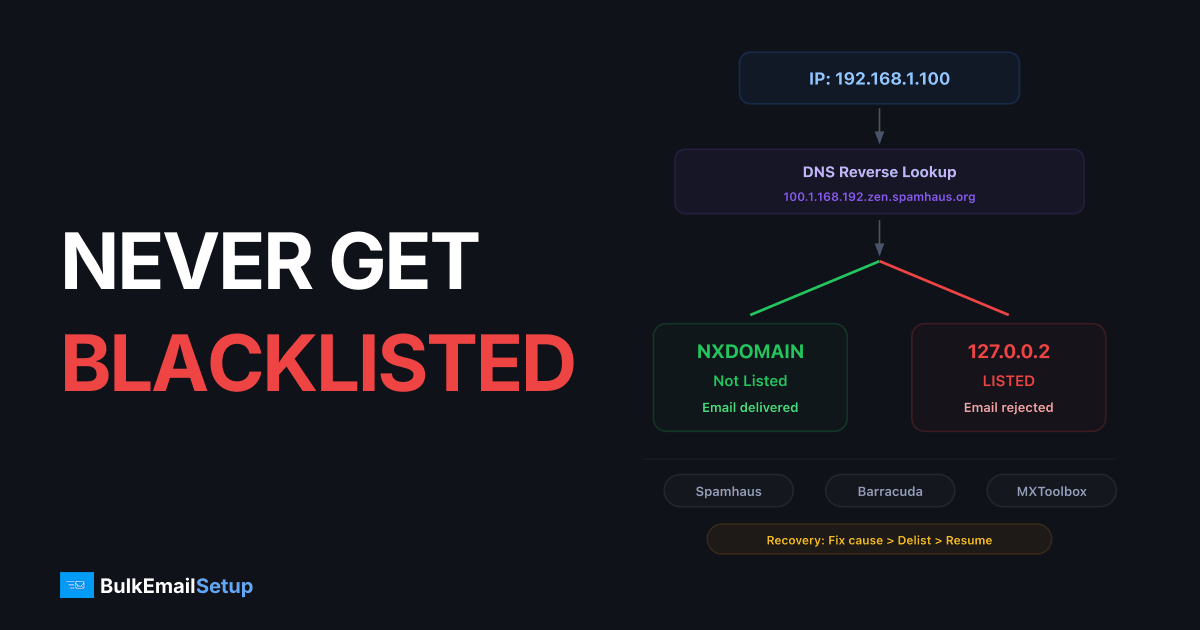
Reverse DNS (rDNS) allows a receiving server to look up the hostname associated with your IP address. This is the reverse of a normal DNS lookup (which resolves a hostname to an IP). ISPs use rDNS as a basic sanity check — legitimate mail servers have PTR records that resolve back to a valid hostname matching their sending domain.
PTR records are set through your VPS or hosting provider, not your domain registrar. Most VPS providers have a control panel option to set reverse DNS. The PTR record should resolve your server's IP to your mail hostname (e.g., mail.yourdomain.com), and that hostname should have an A record pointing back to the same IP. This “forward-confirmed reverse DNS” (FCrDNS) is required by Gmail and most major ISPs.
BIMI (Brand Indicators for Message Identification)
BIMI allows your brand logo to appear next to your email in supported email clients (Gmail, Yahoo, Apple Mail). It is the visual payoff of achieving p=reject DMARC enforcement. BIMI requires three things: a DMARC policy of p=quarantine or p=reject, a Verified Mark Certificate (VMC) from a certified authority, and a BIMI DNS record pointing to your logo.
| BIMI Requirement | Details | Cost |
|---|---|---|
| DMARC p=quarantine or p=reject | Must have enforcement-level DMARC policy | Free (DNS record) |
| SVG logo (tiny-ps profile) | Square SVG logo, no text required, specific SVG profile | Free (design) |
| Verified Mark Certificate (VMC) | Certificate from DigiCert or Entrust proving logo ownership | $1,000-1,500/year |
| BIMI DNS record | TXT record at default._bimi.yourdomain.com | Free (DNS record) |
BIMI is optional and requires a significant investment in the VMC certificate. However, the visual brand presence in Gmail — where over 60% of consumer email is read — can meaningfully improve open rates. Companies that implement BIMI report 10-30% higher open rates due to the trust and recognition that a verified brand logo provides.
Pro Tip
You do not need BIMI to have excellent deliverability. Focus on SPF, DKIM, and DMARC first. BIMI is a branding enhancement that only matters after you have achieved p=reject DMARC enforcement. It is the cherry on top, not the foundation.
Testing and Validating Your Authentication Setup
After configuring SPF, DKIM, and DMARC, you must validate every record before sending any production email. A single typo in a DNS record — a missing semicolon, an extra space, a truncated key — can cause authentication failures that damage your reputation.
Authentication Validation Checklist
- ✓SPF record validates with no errors at mxtoolbox.com/spf.aspx
- ✓SPF DNS lookups are under 10 (check with dmarcian SPF surveyor)
- ✓DKIM public key is published and queryable via dig
- ✓DKIM signature validates on test emails (check email headers)
- ✓DMARC record is syntactically valid at dmarcian.com/dmarc-inspector
- ✓Send test email to Gmail — verify spf=pass, dkim=pass, dmarc=pass in headers
- ✓Send test email to Outlook — verify authentication in headers
- ✓mail-tester.com score is 9/10 or higher
- ✓PTR record resolves correctly (forward-confirmed reverse DNS)
- ✓DMARC aggregate reports are being received at your rua address
Reading Email Headers for Authentication Results
The most reliable way to verify your authentication is to send a test email and examine the headers. In Gmail, click the three dots on any email and select “Show original” to see full headers. Look for the Authentication-Results header, which shows the outcome of each authentication check.
Every line should show pass. If any shows fail, softfail, neutral, or temperror, there is a configuration issue that needs to be fixed before production sending.
Recommended Testing Tools
| Tool | What It Tests | Cost |
|---|---|---|
| mail-tester.com | Overall email score: authentication, content, blacklists, configuration | Free (3 tests/day) or $15/month unlimited |
| MXToolbox SPF/DKIM/DMARC | Individual DNS record validation and syntax checking | Free for basic checks |
| dmarcian | SPF surveyor (lookup counting), DMARC inspector, ongoing monitoring | Free inspector, $100+/month for monitoring |
| Google Postmaster Tools | Domain and IP reputation, authentication rates at Gmail | Free |
| DKIM Validator (dkimvalidator.com) | Send a test email to verify DKIM signature validation | Free |
| Learndmarc.com | Interactive visual explanation of SPF, DKIM, and DMARC results | Free |
Troubleshooting Common Authentication Failures
Authentication failures fall into predictable categories. Here are the most common issues we encounter when auditing email authentication setups, along with their causes and fixes.
Your SPF record exceeds 10 DNS lookups. Fix by replacing 'include' mechanisms with direct ip4/ip6 addresses or using an SPF flattening service. Check lookup count with dmarcian SPF surveyor.
The DKIM public key in DNS does not match the private key on your server. Common cause: DNS provider truncated the key at 255 characters. Verify the full key is published by querying: dig TXT selector._domainkey.yourdomain.com
The email body was modified after signing. Common cause: mailing list software or email forwarding services that add footers or modify content. Solution: use relaxed canonicalization (c=relaxed/relaxed) in your DKIM configuration.
SPF and DKIM pass but DMARC still fails. This means the domain in SPF/DKIM does not align with the From header domain. Ensure your DKIM d= tag matches your From domain, and your SPF envelope sender domain matches your From domain.
Your SPF record uses ~all (tilde) instead of -all (dash). Softfail allows email from unauthorized IPs to be delivered but marked as suspicious. Change to -all (hard fail) for production use.
You published a DMARC record with rua= but are not receiving reports. Check: is the rua email address valid? Some ISPs send reports to a different domain than the one being authenticated — you may need a _dmarc-report DNS record for cross-domain reporting.
DNS has two or more TXT records that start with v=spf1 for the same domain. The SPF specification requires exactly one SPF record per domain. Multiple records cause a PermError. Merge all SPF mechanisms into a single record.
Intermittent DKIM failures usually mean you have multiple sending paths and only some are configured with DKIM. Check all applications and services that send email as your domain — each one needs DKIM signing configured.
Step 1: Check DNS Records
Use dig or MXToolbox to verify your SPF, DKIM, and DMARC records are published correctly and contain no syntax errors.
Step 2: Send Test Email
Send to Gmail and Outlook, then inspect headers for authentication results. All three should show 'pass'.
Step 3: Review DMARC Reports
Wait 24-48 hours for DMARC aggregate reports. They show exactly which senders pass or fail authentication for your domain.
Step 4: Fix and Retest
Address any failures found in headers or reports. Update DNS records, wait for propagation (up to 48 hours), then retest.
Frequently Asked Questions
Do I need all three — SPF, DKIM, and DMARC?
Yes. As of 2026, all three are required by Gmail, Outlook, and Yahoo for bulk senders (5,000+ emails per day). Even if you send lower volumes, having all three significantly improves your inbox placement. SPF alone is insufficient because it does not survive email forwarding. DKIM alone does not tell ISPs what to do on failure. DMARC without SPF and DKIM has nothing to enforce. They work as a system.
How long do DNS changes take to propagate?
DNS propagation typically takes 15 minutes to 48 hours, depending on your TTL (Time to Live) settings and the DNS provider. During initial setup, set your TTL to 300 seconds (5 minutes) so changes propagate quickly. After everything is working, increase TTL to 3600 (1 hour) or 86400 (24 hours) for better caching performance. You can check propagation status at whatsmydns.net.
Can I use SPF without DKIM?
Technically yes, but it is strongly discouraged. SPF breaks when email is forwarded because the forwarding server's IP is not in your SPF record. DKIM survives forwarding because the signature is attached to the message itself. Without DKIM, any forwarded email will fail authentication at the final destination. DMARC requires at least one of SPF or DKIM to pass — having both gives you redundancy.
What DKIM key size should I use?
Use 2048-bit RSA keys. The older 1024-bit keys are still accepted by most ISPs but are considered cryptographically weak and will be deprecated. Some organizations are moving to 4096-bit keys, but these can cause DNS issues because they exceed TXT record size limits at some providers. 2048-bit is the sweet spot for security and compatibility in 2026.
How often should I rotate DKIM keys?
Rotate DKIM keys every 6-12 months as a security best practice. Key rotation ensures that a compromised private key has limited impact. Use date-based selectors (e.g., jan2026, jul2026) to make rotation tracking easy. Always overlap the old and new keys for 1-2 weeks during transition to avoid breaking in-flight email verification.
What should my DMARC policy be if I am just starting?
Start with p=none and aggregate reporting. This collects data without affecting delivery. After 2-4 weeks of clean reports, progress to p=quarantine; pct=10 and gradually increase the percentage. Move to p=reject only after you are confident all legitimate email passes DMARC. The entire progression typically takes 8-12 weeks.
Does email authentication guarantee inbox delivery?
No. Authentication is necessary but not sufficient for inbox delivery. It proves your identity — it does not prove your email is wanted. Deliverability also depends on IP reputation, domain reputation, content quality, engagement rates, and dozens of other factors. Think of authentication as the bouncer checking your ID at the door — it gets you in, but your behavior inside determines if you stay.
Can authentication help with email deliverability for cold email?
Absolutely. Authentication is even more critical for cold email because you have no prior relationship with recipients. ISPs rely heavily on authentication signals when evaluating email from unknown senders. Full SPF, DKIM, and DMARC configuration is a baseline requirement — without it, cold email has near-zero chance of reaching the inbox at major providers like Gmail.
Conclusion: Authentication Is the Foundation of Deliverability
Email authentication with SPF, DKIM, and DMARC is not a one-time setup task — it is an ongoing practice that protects your domain, your recipients, and your deliverability. Properly configured authentication is the single most impactful thing you can do to improve inbox placement, and it costs nothing beyond the time to set it up.
The progression is clear: publish SPF to authorize your sending servers, configure DKIM to sign every outgoing email, deploy DMARC with monitoring first and enforcement later, set up rDNS for your sending IPs, and optionally implement BIMI for brand visibility. Each layer adds trust, and together they form an authentication stack that ISPs reward with better inbox placement.
If you are running a dedicated SMTP server or sending bulk email through any infrastructure, authentication configuration is the first thing to verify — before IP warm-up, before campaign strategy, before anything else. Get authentication right first, and everything that follows becomes easier.
Summary
- SPF authorizes which IPs can send for your domain — stay under 10 DNS lookups
- DKIM signs every email with a cryptographic key — use 2048-bit RSA and rotate every 6-12 months
- DMARC ties SPF and DKIM together with a policy — progress from p=none to p=reject over 8-12 weeks
- PTR/rDNS records must match your sending hostname — set these through your VPS provider
- Test with mail-tester.com and verify email headers show spf=pass, dkim=pass, dmarc=pass
- Google, Microsoft, and Yahoo require all three protocols for bulk senders as of 2024
- BIMI adds your brand logo in supported clients — requires p=reject DMARC and a VMC certificate
- Monitor DMARC reports continuously to catch new unauthorized senders and authentication failures
Need help configuring email authentication for your sending infrastructure? Our managed plans include complete SPF, DKIM, and DMARC configuration, rDNS setup, and ongoing authentication monitoring. Or contact us for a free authentication audit of your current domain setup.